How Secure is CMMS Software?

Safeguards of Maintenance Operations
Where every byte of data can unlock unprecedented efficiencies and insights, Computerized Maintenance Management Systems (CMMS) has emerged as a beacon of operational excellence. These sophisticated platforms empower maintenance teams to orchestrate their workflows with unparalleled precision, transforming routine upkeep into a strategic advantage. Yet, amid this digital expanse, a shadow looms large: the ever-present risk of cyber threats and data breaches. This exploration delves into the fortress of CMMS software security, shedding light on the safeguards that protect the lifeblood of maintenance operations.
The Veil of CMMS Software Security
Imagine for a moment the heart of your operations beating in sync with the digital pulse of a CMMS, streamlining preventive maintenance schedules and monitoring asset health with clinical precision. But this digital heart is vulnerable; the technology that propels efficiency forward also paints a target for cyber predators. A breach can unravel in moments, erasing critical data, paralyzing operations, and tarnishing reputations in an unforgiving digital landscape. Thus, arming oneself with robust CMMS security measures transcends benefit—it becomes a shield essential for survival.
The Vanguard of CMMS Security Features

A number of factors stand as the key safeguards of CMMS data:
Data Encryption and Protection: At the vanguard of CMMS defense lies data encryption, a silent guardian that renders data cryptic to prying eyes. Whether data is at rest within the system or traversing the digital ether, encryption ensures it remains an enigma, accessible only to those who hold the key. Embracing industry-standard encryption protocols like AES-256, CMMS platforms fortify their vaults against intrusion. Moreover, compliance with stringent data protection mandates like the GDPR acts as an additional bulwark, significantly diminishing the specter of data breaches.
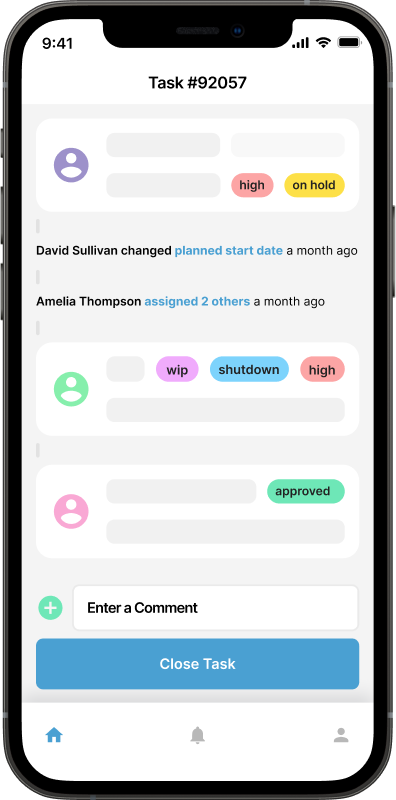
User Access Control and Authentication: The sanctum of your CMMS is further secured by intricate access controls, delineating who can gaze upon or alter the data. Adopting multi-factor authentication (MFA) weaves an extra layer of security, ensuring that only verified individuals can penetrate the system's defenses. This mechanism is crucial, whether the CMMS sails in the cloud or stands guard on-premise, ensuring that the gatekeepers of your data fortress are always vigilant.
Compliance Standards and Data Privacy: A CMMS's allegiance to recognized security and compliance standards, such as SOC 2 and ISO 27001, signals a commitment to a fortress impervious to threats. These standards are the bedrock upon which secure operational protocols, risk management strategies, and information-safeguarding practices are built. A CMMS that honors data privacy aligns with global regulations and respects user data's sanctity, fortifying trust in a digital age.
The Keystone of Secure CMMS Implementation
Even the most fortified CMMS requires the vigilance of its stewards to ensure its defenses remain impenetrable. Regular security audits are conducted by seasoned professionals, and unearth vulnerabilities are hidden within the digital shadows. Empowering employees with cybersecurity awareness training equips them with the knowledge to thwart phishing and other digital menaces. Moreover, establishing robust internal policies on data management, access control, and password protocols is the bedrock of a secure CMMS ecosystem. Leveraging the full spectrum of built-in security functionalities, like role-based access control (RBAC), ensures that every layer of the CMMS is shielded against intrusion.
The security of CMMS software stands as a pillar upon which the sanctity of maintenance operations rests. By championing systems endowed with advanced security measures—be it through sophisticated data encryption, rigorous user authentication, or adherence to global security standards—organizations can shield their operational heart against the disruption of cyber threats. However, this shield is not borne by technology alone; it is a covenant forged in organizations' collective resolve to cultivate a cybersecurity awareness culture. As we navigate the digital currents, anchor your choices in security, for in protecting our data, we protect the very integrity of our operations.
Further Reading

What is CMMS?
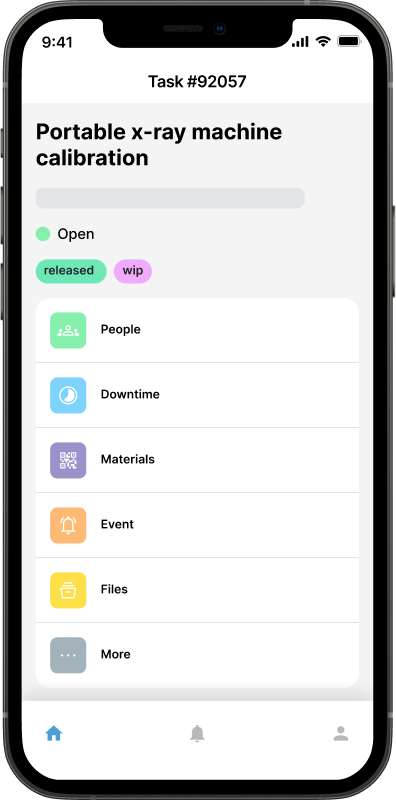
A Computerized Maintenance Management System (CMMS) is a software solution that streamlines and automates maintenance management processes, including work orders, preventive maintenance, asset tracking, and inventory management, to optimize the efficiency and performance of organizational assets. But let's dig into the details...
Read more →
Benefits of CMMS
CMMS will aid and inform technicians out in the field, as well as decision makers, on maintenance work that has been done, will be done soon, or is planned to be done in the future. Broadly speaking, the benefits of CMMS can be broken down into three categories: management; visibility; and cost control.
Read more →
What is the 75% Maintenance Rule in Asset Management: When to Repair or Replace
What exactly is the 75% maintenance rule, how is it applied, and why should it be integrated into your Computerized Maintenance Management System (CMMS)?
Read more →